Context Over Patterns: How SnortML and Agentic AI Are Redefining Intrusion Detection
Intrusion detection has long relied on matching network traffic against known threat signatures—a method that works well for yesterday’s attacks but struggles with today’s subtle, context-dependent threats. With the rise of machine learning and autonomous agents, the fundamental question is shifting from “does this packet match a known pattern?” to “does this behavior make sense in context?” This Q&A explores how SnortML and agentic AI transform detection into a reasoning engine.
What is signature-based detection and why is it changing?
Signature-based detection works by comparing network traffic against predefined fingerprints of known attacks. It’s fast, reliable for known threats, and easy to implement. However, it cannot detect zero-day exploits or attacks that intentionally vary from known patterns. The core question it answers is static: “Does this match a known pattern?” As attackers become more sophisticated, this approach yields too many false negatives because it lacks understanding of the broader context—like the user’s typical behavior or the state of the system. The industry is now shifting toward systems that ask “does this actually make sense in context?”
How does SnortML change the question from pattern matching to contextual reasoning?
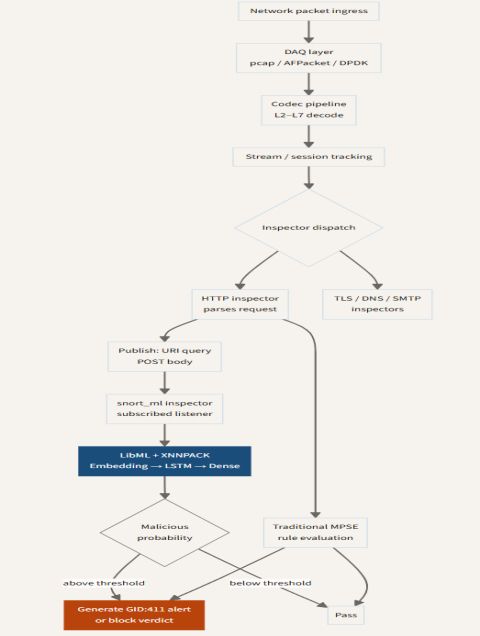
SnortML extends the classic Snort IDS by integrating machine learning models. Instead of only firing when a byte sequence matches a rule, SnortML analyzes traffic for probabilistic anomalies. For example, it can learn what “normal” network flows look like and flag deviations that could indicate an attack even if no signature exists. This shifts the detection logic from binary matching to continuous scoring. The output is not just an alert but a measure of how anomalous—or risky—a session appears relative to learned baselines. By embedding ML directly into the detection pipeline, SnortML enables the system to answer “does this make sense” in near real time.
What is agentic AI and how does it apply to intrusion detection?
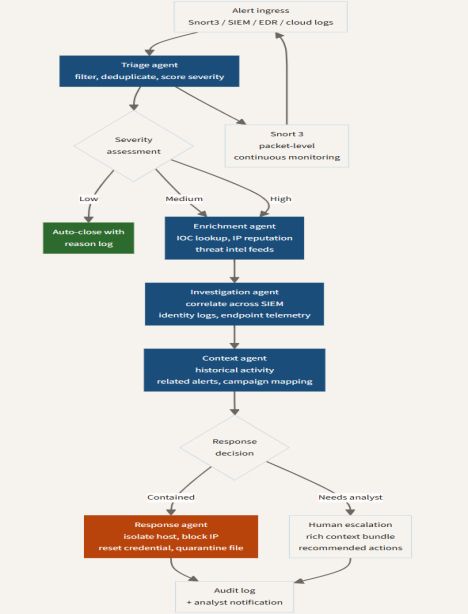
Agentic AI refers to autonomous software agents that perceive their environment, set goals, and take actions to achieve those goals without human intervention. In intrusion detection, an agentic system might continuously monitor network traffic, correlate events across multiple sensors, and dynamically alter detection thresholds or block traffic based on its own reasoning. Unlike static rule sets, these agents adapt and learn from new data. For instance, if an agent detects several low‑risk anomalies together, it could escalate to a higher alert level autonomously. This moves IDS from a passive “watchdog” role to an active, reasoning participant in security operations.
Why does context matter more than pure pattern matching?
Context allows a detection system to distinguish between a genuine attack and a false alarm. A packet that matches a known exploit signature might still be benign if it occurs in a controlled test environment or as part of a legitimate update. Conversely, a sequence of seemingly normal operations—like a user accessing unusual servers at odd times—can signal a breach when viewed in context. Pattern matching alone cannot capture relationships between events, user roles, or time of day. By incorporating contextual features (e.g., user identity, asset criticality, historical behavior), detectors drastically reduce false positives and uncover sophisticated threats that never trigger a single signature.
How do SnortML and agentic AI work together in modern IDS architecture?
Modern IDS architecture often layers multiple detection methods. Signature‑based engines handle high‑confidence, low‑fidelity detections. SnortML injects a layer of statistical analysis that feeds anomaly scores into a centralized event stream. An agentic AI layer then governs correlation and decision‑making: it ingests alerts from both signature and ML sources, enriches them with external threat intelligence, and decides on an appropriate response (e.g., drop, log, quarantine). The agent can also tune SnortML thresholds or activate new signatures autonomously. This creates a feedback loop where the system continuously improves its contextual understanding without constant human tuning.
What is the future of intrusion detection with these evolving technologies?
Future IDS will likely treat detection as a continuous process rather than a point‑in‑time match. We anticipate fully autonomous agents that patrol enterprise networks like digital guards, using reinforcement learning to optimize detection strategies. SnortML‑type models will become stream‑based and self‑updating, retraining on new traffic patterns in real time. The key challenge remains explainability: security teams must trust the AI’s reasoning. Solutions will combine signature speed with ML adaptability and agentic autonomy, ultimately answering the question “does this behavior make sense” with high accuracy and minimal false positives. Integration with SOAR platforms and automated playbooks will make dynamic response seamless.